Most companies in the US today have BYOD policies within the workplace. Integrating a BYOD policy can streamline operations, cut costs, increase efficiency and productivity, and bring joy within your team.
However, staying on top of device security issues is vital, as breaches could harm your operations, create data security risks, financial risks, and concerns over privacy and your company’s reputation.
The key lies not only in embracing technology advancement but also managing it wisely. This balance ensures your company harnesses the power of personal device use, while maintaining top-notch security measures.

Essential Practices with a Workplace BYOD Policy
Whether or not employees are already using personal electronic devices in the workplace, companies should review their BYOD policies. The best practices for implementing BYOD in the workplace include the following;
- Mobile Device Management (MDM) system in place to ensure security and manageability
- Privacy Measures for both company data and employee protection for how much access the company has to a personal device
- System Integration to ensure devices are compatible with company networks, applications, operations, and security systems
- Technical Support both proactive and responsive with real-time remote support
- Regular training and updates including security awareness training, privacy and password management
- Exit strategies for removing company data from a device when an employee leaves the company
Utilizing Faraday Bags for Security and Privacy
A single unsecure device, like a cell phone or tablet, can create an entry point for a cybercriminal to wreak havoc for an entire company or organization.
Using a Faraday bag, whether that be a pouch, cell phone bag, or sleeve for your tablet or laptop, instantly blocks cellular, WiFi, Bluetooth, RFID/NFC, GPS, SAT/NAV signals as well as remote access to your device’s camera and microphone.
Using a Faraday bag, whether that be a pouch, cell phone bag, or protection fabric sleeve for phones, laptops, tablets to block any signal including cellular, WiFi, Bluetooth, RFID/NFC, GPS, SAT/NAV signals as well as remote access to your device’s camera and microphone.
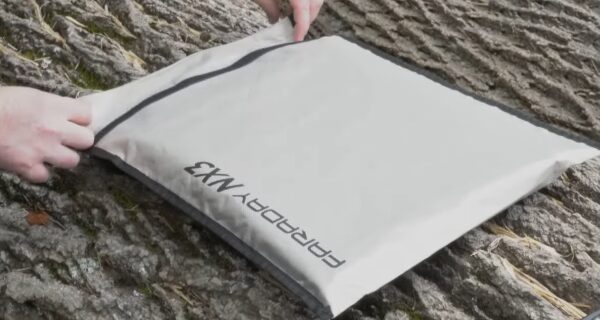
This is an easy and effective way to create digital security, protecting company data, financial information, personnel and client information, passwords, and more.
Faraday bags are used by forensic investigators, law enforcement, military, political leaders, and smart businesses and corporations to secure valuable information.
Identifying and Countering BYOD Risks
Despite the many conveniences and benefits of using personal laptops, tablets, and cell phones in the office, when employees use their own devices for work, they bring challenges and potential risks.
Security Breaches
One of the main concerns is security breaches. Personal devices might not have the same level of security as company devices, making them more susceptible to data breaches and unauthorized access.
Imagine if a rogue app on an employee’s personal device accessed sensitive company data without anyone realizing it. This could lead to serious consequences for the company.
According to lastpass.com 45% of employees don’t bother to change their password after a data breach.
To counter these risks, it’s imperative for organizations to invest in regular security training for employees and implement strong data security controls.
These measures can help employees understand the potential risks associated with using personal devices for work, and also empower them to take necessary precautions. Additionally, robust data security solutions are vital in classifying, protecting, and monitoring interactions with data.

Companies can use encryption software to secure data on personal devices and ensure that sensitive information remains protected. In addition, multi-factor authentication can add an extra layer of security when accessing company resources from personal devices.
Data Integrity
Aside from security breaches, BYOD also poses risks to data integrity and confidentiality. Organizations need to take proactive steps to address these risks.
Imagine a scenario where an employee accidentally leaks confidential information by saving it on their personal cloud storage accessible to other apps on their device. This could compromise the integrity of sensitive data and lead to significant repercussions for the organization.
To protect against these risks, companies must implement robust data security solutions that safeguard the integrity and confidentiality of their data. This includes classifying sensitive data, implementing encryption protocols, and monitoring interactions with data to detect unauthorized access or breaches.
Furthermore, establishing clear guidelines and policies regarding the type of data that can be accessed and stored on personal devices is essential.
Employees should be made aware of these policies through comprehensive training programs to ensure that they understand their responsibility in maintaining the integrity and confidentiality of company data.
Understanding the potential risks associated with BYOD is just the first step; mitigating these risks through proactive measures is vital in ensuring a secure and productive work environment.
Lost or Stolen Devices
When using personal devices for work purposes, you risk unauthorized access to company systems and sensitive business information ending up in a stranger’s hands.

Since personal devices are taken everywhere – from restaurants and shops to large arenas and theatres, on public transportation, and any public place you can think of, there is a high risk of lost or stolen personal electronics.
According to Asurion data, in 2022 more than 11,500 cell phones are lost or stolen every single day.
The best way to safeguard against this risk is to use encryption software to protect data stored on personal devices and any information transmitted to company networks and authentication measures to prevent unauthorized access to company networks and data.
Wiping devices remotely of sensitive company data will also be necessary in this situation to protect against data and privacy breaches.
